#lockbit #ransomware #cybersecurity #fraud #cyberextortion

Fig. 1. Dmitry Yuryevich Khoroshev, aka LockBitSupp.[1]
Law enforcement agencies spanning the United States, United Kingdom, and Australia have collectively pinpointed Russian national Dmitry Yuryevich Khoroshev as the suspected architect behind the infamous LockBit ransomware crime gang, operating under the moniker LockBitSupp. The government asserts LockBit victims span a wide array of entities, including individuals, small businesses, multinational corporations, hospitals, schools, nonprofit organizations, critical infrastructure, and government and law enforcement agencies. They are responsible for draining an estimated $500 million from its victims over an extensive hacking spree including:[2]
1) 148 built attacks.
2) 119 engaged in negotiations with victims, meaning they definitely deployed attacks.
3) Of the 119 who began negotiations, there are 39 who appear not to have ever received a ransom payment.
4) 75 did not engage in any negotiation, so also appear not to have received any ransom payments.
The group has long evaded identification, with LockBitSupp shrouded in online anonymity due to multiple VPNs, VMs, and fake pass-through names and entities. He was so bold that he even offered a $10 million reward to anyone that could reveal his identity.[3]
This revelation comes in the wake of a substantial operation by UK law enforcement, which infiltrated LockBit’s systems, executed multiple arrests, dismantled its infrastructure, and intercepted internal communications, effectively reducing LockBit’s criminal operations — but not stopping or deterring them. This was dubbed Operation Cronos and initiated in February 2024.[4]
Details disclosed by the United States Office of Foreign Assets Control (OFAC) reveal Khoroshev, aged 31 and residing in Russia, is under sanction, with his designation including various email and cryptocurrency addresses, alongside details from his Russian passport. Furthermore, the United States has filed a comprehensive indictment against him.[5] He also faces 26 criminal charges, including extortion and hacking, carrying a cumulative maximum penalty of 185 years in prison. The Justice Department has also issued a $10 million bounty for information leading to his arrest.
‘”This identification and charging of Khoroshev mark a significant milestone,” remarked Principal Deputy Assistant Attorney General Nicole Argentieri in a statement on Tuesday. “Through the meticulous efforts of our investigators and prosecutors, we have unveiled the individual behind LockBitSupp.”’[6]
According to the indictment, Khoroshev is alleged to have served as the developer and administrator of the LockBit ransomware group from its inception in September 2019 through May 2024, typically receiving a 20 percent share of each ransom payment extorted from LockBit victims.
Federal authorities utilized LockBit’s existing victim shaming website layout to disseminate press releases and provide free decryption tools. Following the FBI’s intervention, LockBitSupp reassured partners and affiliates via Russian cybercrime forums that the ransomware operation remained fully operational. Additional darknet websites were launched, promising the release of data stolen from several LockBit victims prior to the FBI’s intervention.
Fig. 2. Lockbit Victim Shaming Portal With FBI Takeover.[7]

Despite LockBitSupp’s claims of invincibility, law enforcement efforts have made strides. The group’s modus operandi included “double extortion,” demanding separate ransom payments for both unlocking hijacked systems and promising to delete stolen data. However, the Justice Department asserts LockBit never followed through on deleting victim data, regardless of ransom payments made — all the more reason why you should not pay or trust these types.
Khoroshev marks the sixth individual indicted as an active member of LockBit. Among those indicted are Russian nationals Artur Sungatov and Ivan Gennadievich Kondratyev, alias “Bassterlord,” charged with deploying LockBit against targets in various industries across multiple countries.[8]
Lastly, leading threat intel consultancy Recorded Future facilitated an interview with LockbitSupp over an encrypted app via the dark web, where he said they got the wrong guy, among other things. [9] The interview is linked here thanks to hard work of The Record from Recorded Future News and Dmitry Smilyanets!
Disclaimer:
All citations and statements are from publicly available reports. No private info was disclosed in this article. Feedback is welcome. Attempts to retaliate against or censor my research and/or writing will be reported (you will be blocked). This was drafted with the current info, and future info could change things.
About the Author:
Jeremy Swenson is a disruptive-thinking security entrepreneur, futurist/researcher, and senior management tech risk consultant. He is a frequent speaker, published writer, podcaster, and even does some pro bono consulting in these areas. He holds an MBA from St. Mary’s University of MN, an MSST (Master of Science in Security Technologies) degree from the University of Minnesota, and a BA in political science from the University of Wisconsin Eau Claire. He is an alum of the Federal Reserve Secure Payment Task Force, the Crystal, Robbinsdale and New Hope Citizens Police Academy, and the Minneapolis FBI Citizens Academy.
References:
[1] Goodin, Dan. “Ransomware mastermind LockBitSupp reveled in his anonymity—now he’s been ID’d.” Ars Technical. 05/07/24. https://arstechnica.com/security/2024/05/the-mastermind-of-the-prolific-ransomware-group-lockbit-has-finally-been-unmasked/
[2] National Crime Agency (NCA). “LockBit leader unmasked and sanctioned.” Viewed 05/10/24. https://www.nationalcrimeagency.gov.uk/news/lockbit-leader-unmasked-and-sanctioned
[3] Burgess, Matt. “The Alleged LockBit Ransomware Mastermind Has Been Identified.” Wired. 05/07/24. https://www.wired.com/story/lockbitsupp-lockbit-ransomware/
[4] Boyton, Christopher. “Unveiling the Fallout: Operation Cronos’ Impact on LockBit Following Landmark Disruption.” Trend Micro. 04/03/24. https://www.trendmicro.com/en_us/research/24/d/operation-cronos-aftermath.html
[5] US Attorneys Office: NJ. “U.S. Charges Russian National with Developing and Operating Lockbit Ransomware.” 05/07/24. https://www.justice.gov/usao-nj/pr/us-charges-russian-national-developing-and-operating-lockbit-ransomware
[6] Sean Powers, Sean; Abdul-Malik, Jade; Temple Raston, Dina. “In interview, LockbitSupp says authorities outed the wrong guy.” The Record by Recorded Future. 05/09/24. https://therecord.media/lockbitsupp-interview-ransomware-cybercrime-lockbit
[7] Boyton, Christopher. “Unveiling the Fallout: Operation Cronos’ Impact on LockBit Following Landmark Disruption.” Trend Micro. 04/03/24. https://www.trendmicro.com/en_us/research/24/d/operation-cronos-aftermath.html
[8] FlashPoint. “Indictment-USA-v.-Ivan-Kondratyev.” 05/17/22. https://flashpoint.io/wp-content/uploads/Indictment-USA-v.-Ivan-Kondratyev.pdf
[9] Sean Powers, Sean; Abdul-Malik, Jade; Temple Raston, Dina. “In interview, LockbitSupp says authorities outed the wrong guy.” The Record by Recorded Future. 05/09/24. https://therecord.media/lockbitsupp-interview-ransomware-cybercrime-lockbit









 Ransomware is on the rise and is going after more victims with little to no defenses, small to medium-small sized businesses and even quiet non-profits. Here are a few tools with a valid track record of stopping and removing 3 common types of ransomware.
Ransomware is on the rise and is going after more victims with little to no defenses, small to medium-small sized businesses and even quiet non-profits. Here are a few tools with a valid track record of stopping and removing 3 common types of ransomware.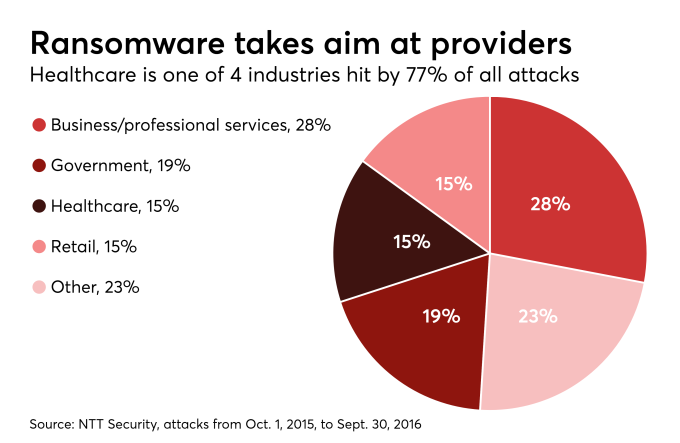 As per Jessica Davis of HealthcareITnews, “SamSam is the virus that
As per Jessica Davis of HealthcareITnews, “SamSam is the virus that 