Fig. 1. Stock Virus Infographic, 2023.
#smbinfosec #cyberrisk #techrisk #techinnovation #infosec #infosec #cloudcomputing
#cyberdefense #disinformation #cio #ciso #cto #tech #ransomwareattack #123backup
1) Educate Employees About Cyber Threats and Hold Them Accountable:
Educate your employees about online threats and how to protect your business’s data, including safe use of social networking sites. Depending on the nature of your business, employees might be introducing competitors to sensitive details about your firm’s internal business. Employees should be informed about how to post online in a way that does not reveal any trade secrets to the public or competing businesses. Use games with training and hold everyone accountable to security policies and procedures. This needs to be embedded in the culture of your company. Register for free DHS cyber training here and/or use the free DHS SMB cyber resource toolkit. Most importantly, sign up for DHS CISA e-mail alerts specific to your company and industry needs and review the alerts – Sign up here. Use the free DHS developed CSET (Cybersecurity Evaluation Tool) to assess your security posture – High, Med, or Low. CSET is downloadable here.
2) Protect Against Viruses, Spyware, and Other Malicious Code:
Make sure each of your business’s computers are equipped with antivirus software and antispyware and updated regularly. Such software is readily available online from a variety of vendors. All software vendors regularly provide patches and updates to their products to correct security problems and improve functionality. Configure all software to install updates automatically. Especially watch out for freeware that contains malvertising. Make sure submission forms can block spam and can block code execution (cross-side scripting attacks).
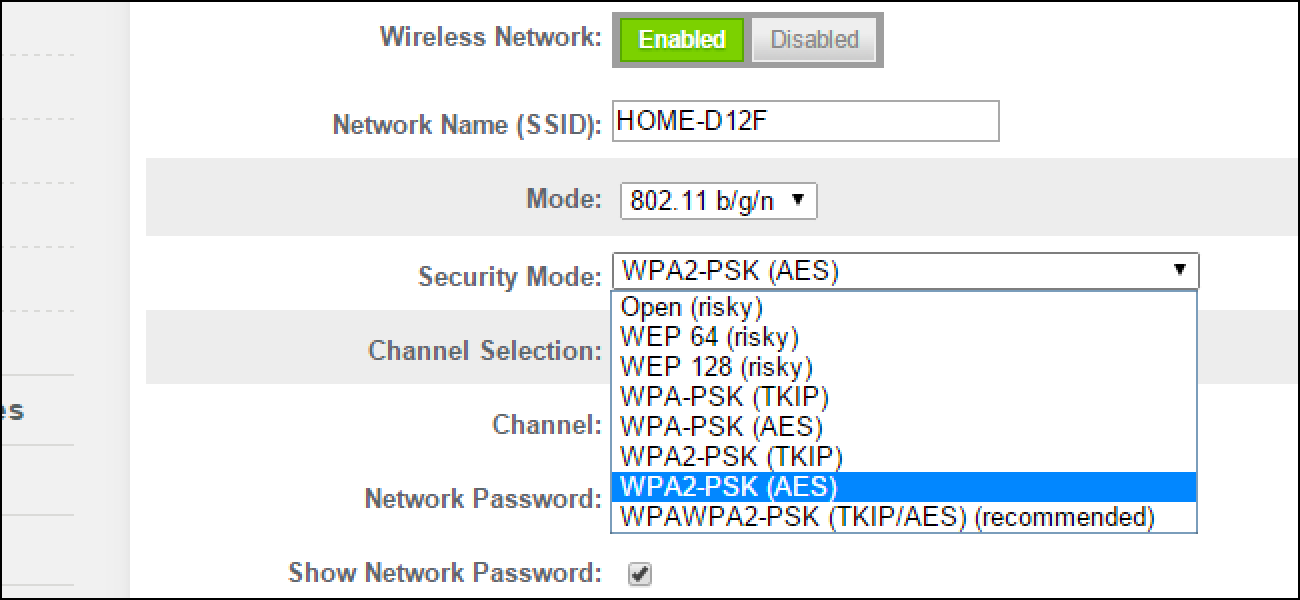
3) Secure Your Networks:
Safeguard your Internet connection by using a firewall and encrypting information. If you have a Wi-Fi network, make sure it is secure and hidden – not publicly broadcasted. To hide your Wi-Fi network, set up your wireless access point or router so it does not broadcast the network name, known as the Service Set Identifier (SSID). Also, have a secure strong password to protect access to the router. (xbeithyg18695843%&*&RELxu75IGO) — example. Lastly, use a VPN (virtual private network) to encrypt data in transit, especially when working from home.
4) Control Physical Access to Computers and Network Components:
Prevent access or use of business computers by unauthorized individuals. Laptops can be particularly easy targets for theft or can be lost, so lock them up when unattended. Make sure a separate user account is created for each employee and require strong passwords. Administrative privileges should only be given to trusted IT staff and key personnel — with approval records.
5) Create A Mobile Device Protection Plan:
Require users to password-protect their devices, encrypt their data, and install security apps to prevent criminals from stealing information while the phone is on public networks. Use a containerization application to separate personal data from company data. Be sure to set reporting procedures for lost or stolen equipment.
6) Establish Security Practices and Policies to Protect Sensitive Information:
Establish policies on how employees should handle and protect personally identifiable information and other sensitive data. Clearly outline the consequences of violating your business’s cybersecurity policies and who is accountable. Base your security strategy significantly on the NIST Cybersecurity Framework 1.1: Identify, Detect Defend, Respond, and Recover — a respected standard that easy to understand (Fig. 1). The NIST Cybersecurity Framework Small Business Resources are linked here.

Fig. 2. NIST CSF Domains and Sub Areas, NIST, 2022.
7) Employ Best Practices on Payment Cards:
Work with your banks or card processors to ensure the most trusted and validated tools and anti-fraud services are being used. You may also have additional security obligations related to agreements with your bank or processor. Isolate payment systems from other, less secure programs and do not use the same computer to process payments and surf the internet. Outsource some or all of it and know where your risk responsibility ends.
8) Make Backup Copies of Important Business Data and Use Encryption When Possible:
Regularly backup the data on all computers. Critical data includes word processing documents, electronic spreadsheets, databases, financial files, human resources files, and accounts receivable/payable files. Back up data automatically if possible, or at least weekly, and store the copies either offsite or on the cloud. Having all key files backed up via the 3-2-1 rule — three copies of files in two different media forms with one offsite — thus reducing ransomware attack damage.
9) Use A Password Management Tool and Strong Passwords:
Another way to stay safe is by setting passwords that are longer, complex, and thus hard to guess. Additionally, they can be stored and encrypted for safekeeping using a well-regarded password vault and management tool. This tool can also help you to set strong passwords and can auto-fill them with each login — if you select that option. Yet using just the password vaulting tool is all that is recommended. Doing these two things makes it difficult for hackers to steal passwords or access your accounts.
10) Use Only Whitelisted Sites Not Blacklisted Ones or Ones Found Via the Dark Web:
Use only approved whitelisted platforms and sites that do not expose you to data leakages or intrusion on your privacy. Whitelisting is the practice of explicitly allowing some identified websites access to a particular privilege, service, or access. Backlisting is blocking certain sites or privileges. If a site does not assure your privacy, do not even sign up let alone participate.
About the Author:
Jeremy Swenson is a disruptive-thinking security entrepreneur, futurist/researcher, and senior management tech risk consultant. Over 17 years he has held progressive roles at many banks, insurance companies, retailers, healthcare orgs, and even governments including being a member of the Federal Reserve Secure Payment Task Force. Organizations relish in his ability to bridge gaps and flesh out hidden risk management solutions while at the same time improving processes. He is a frequent speaker, published writer, podcaster, and even does some pro bono consulting in these areas. As a futurist, his writings on digital currency, the Target data breach, and Google combining Google + video chat with Google Hangouts video chat have been validated by many. He holds an MBA from St. Mary’s University of MN, an MSST (Master of Science in Security Technologies) degree from the University of Minnesota, and a BA in political science from the University of Wisconsin Eau Claire.

 They can also use the CSET (Cyber Security Evaluation Tool), which is a free customizable multi-framework DHS created general cyber security assessment. A 2017 report published by Keeper Security and the Ponemon Institute found more than 50% of small and medium business had been breached in the past 12 months, but only 14% of them rated their ability to defend against cyber-threats as “highly effective” (
They can also use the CSET (Cyber Security Evaluation Tool), which is a free customizable multi-framework DHS created general cyber security assessment. A 2017 report published by Keeper Security and the Ponemon Institute found more than 50% of small and medium business had been breached in the past 12 months, but only 14% of them rated their ability to defend against cyber-threats as “highly effective” (