1) Crimeware
This is designed to fraudulently obtain financial gain from either the affected user or third parties by emptying bank accounts, or trading confidential data, etc. Crimeware most often starts with advanced social engineering which results in disclosed info that leads to the crimeware being installed via programs that run on botnets which are zombie computers in distant places used to hide the fraudsters I.P (internet protocol) trail. Usually the victim does not know they have crimeware on their computer until they start to see weird bank charges or the like, or an I.T. professional points it out to them. Often times it masquerades as fake but real looking antivirus software demanding your credit card info in an effort to then commit fraud with that info.
2) Cyber-Espionage
The term generally refers to the deployment of viruses that clandestinely observe or destroy data in the computer systems of government agencies and large enterprises – unauthorized spying by computer, tablet, or phone. Antivirus maker Symantec described one noteworthy example where the U.S. Gov’t made a worm to disable Iran’s nuclear reactors arguably in the name of international security (Fig. 1).
“Stuxnet is a computer worm that targets industrial control systems that are used to monitor and control large scale industrial facilities like power plants, dams, waste processing systems and similar operations. It allows the attackers to take control of these systems without the operators knowing. This is the first attack we’ve seen that allows hackers to manipulate real-world equipment, which makes it very dangerous. It’s like nothing we’ve seen before – both in what it does, and how it came to exist. It is the first computer virus to be able to wreak havoc in the physical world. It is sophisticated, well-funded, and there are not many groups that could pull this kind of threat off. It is also the first cyberattack we’ve seen specifically targeting industrial control systems” (Accessed 03/20/16, Norton Stuxnet Review).
Richard Clarke is the former National Coordinator for Security, Infrastructure Protection and Counter-terrorism for the United States and he commentated on Stuxnet and cyber war generally in this Economist Interview from 2013.
Fig.1.
3) Denial of Service (DoS) Attacks
A DoS attack attempts to deny legitimate users access to a particular resource by exploiting bugs in a specific operating system or vulnerabilities in the TCP/IP implementation (internet protocols) via a botnet of zombie computers in remote areas (Fig. 2). This allows one host (usually a server or router) to send a flood of network traffic to another host (Fig. 3.). By flooding the network connection, the target machine is unable to process legitimate requests for data. Thus the targeted computers may crash or disconnect from the internet from resource exhaustion – consuming all bandwidth or disk space, etc (Fig. 3.). In some cases they are not very harmful, because once you restart the crashed computer everything is on track again; in other cases they can be disasters, especially when you run a corporate network or ISP (internet service provider).
Fig. 2. Fig. 3.
4) Insider and Privilege Misuse
Server administrators, network engineers, outsourced cloud workers, developers, I.T. security workers, and database administrators are given privileges to access many or all aspects of a company’s IT infrastructure. Companies need these privileged users because they understand source code, technical architecture, file systems and other assets that allow them to upgrade and maintain the systems; yet this presents a potential security risk.
With the ability to easily get around controls that restrict other non-privileged users they sometimes abuse what should be temporary access privileges to perform tasks. This can put customer data, corporate trade secrets, and unreleased product info at risk. Savvy companies implement multi-layered approvals, advanced usage monitoring, 2 or 3 step authentication, and a strict need to know policy with an intelligible oversight process.
5) Miscellaneous Errors
This is basically an employee or customer doing something stupid and unintentional that results in a partial or full security breach of an information asset. This does not include lost devices as that is grouped with theft – this is a smaller category. The 2014 Verizon Enterprise Data Breach Investigation Report gives an example of this category as follows:
“Misdelivery (sending paper documents or emails to the wrong recipient) is the most frequently seen error resulting in data disclosure. One of the more common examples is a mass mailing where the documents and envelopes are out of sync (off-by-one) and sensitive documents are sent to the wrong recipient” (Accessed 02/21/16, Page 29).
6) Payment Card Skimmers
This is a method where thieves steal your credit card information at the card terminals, often at bars, restaurants, gas stations, sometimes at bank ATMs, and especially where there is low light, no cameras, or anything to discourage the criminal from tampering with the card terminal.
Corrupt employees can have a skimmer stashed out of sight or crooks can install hidden skimmers on a gas pump. Skimmers are small devices that can scan and save credit card data from the magnetic stripe (Fig. 4.). After the card slides through the skimmer, the data is saved, and the crooks usually then sell the information through the internet or if they really want to be secure the Darknet which is a secure non-mainstream internet that requires a special browser or plug-in to access. After this counterfeit cards are made, then bogus charges show up, and the bank eats the costs which unfortunately drives up the cost of banking for everyone else. Also, some skimmers have mini cameras which record the pin numbers typed at ATM machines for a more aggressive type of fraud (Fig. 5.). Here are two images of skimmer technologies:
Fig 4. Fig 5.

7) Physical Theft and Loss
This includes armed robbery, theft by accident, and/or any type of device or data lost. Although some of the stolen or lost items may never end up breached or used for fraud sometime they are depending on what device and/or what data is on that device and/or if it was encrypted or not, or if it the data could be deleted remotely, etc.
8) Point of Sale Intrusions
See my 2014 post on the Target Data Breach here for a good example.
9) Web App Attacks
These incidents were carried out primarily via manipulation of vulnerabilities in input validation and authentication affecting common content management systems like Joomla, Magento, SiteCore, WordPress, and Drupal.
According to the 2015 Verizon Data Breach Investigation Report these types of attacks are not only a reliable method for hackers, but also fast with 60% of the compromises taking a few minutes or less(Accessed 02/21/16). With web applications commonly serving as an organization’s public face to the Internet, the ease of exploiting web-based vulnerabilities is alarming (Accessed 02/21/16, 2015 Verizon Data Breach Investigation Report). According to The Open Web Application Security Project these are two common types Web App weaknesses (Accessed 02/21/16, 2013, OWASP 10 Most Critical Web Application Security Risks):
“i) Injection flaws, such as SQL, OS, and LDAP injection occur when untrusted data is sent to an interpreter as part of a command or query. The attacker’s hostile data can trick the interpreter into executing unintended commands or accessing data without proper authorization.
ii) XSS flaws occur whenever an application takes untrusted data and sends it to a web browser without proper validation or escaping (Fig. 6.). XSS allows attackers to execute scripts in the victim’s browser which can hijack user sessions, deface web sites, or redirect the user to malicious sites access unauthorized pages”.
Fig. 6.

Jeremy Swenson, MBA is a seasoned, Intel certified, retail technology marketing and training representatives on assignment at Best Buy for clients including Intel, Trend Micro, Adobe, and others. He also doubles as a Sr. business analyst and project management consultant. Tweet to him @jer_Swenson.

 Last time Cassem and I commentated on this situation was August of last year when Microsoft was high on the release of Windows 10, arguably their best operating system in a decade but not without risk. In our last piece we valued many aspects of Microsoft’s products including the Cloud, SharePoint, and Windows 10 for business users, but we only began to address the full story. Yet our prior conclusion that Microsoft as a company is undervalued is unchanged because they have so many successful products including Server, Exchange, Visual Studio, System Center, Dynamics, and SharePoint, in spite of their phones weaknesses.
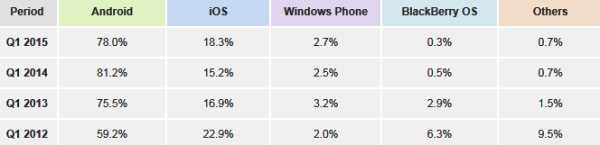
Last time Cassem and I commentated on this situation was August of last year when Microsoft was high on the release of Windows 10, arguably their best operating system in a decade but not without risk. In our last piece we valued many aspects of Microsoft’s products including the Cloud, SharePoint, and Windows 10 for business users, but we only began to address the full story. Yet our prior conclusion that Microsoft as a company is undervalued is unchanged because they have so many successful products including Server, Exchange, Visual Studio, System Center, Dynamics, and SharePoint, in spite of their phones weaknesses. With 53.3% (Fig. 1.) of the phone OS market share there are a few things that Android got right. The integration of Google Calendar is easy, useful, and free. Conversely, on a Windows phone, the integration of Microsoft Outlook is awkward, overly optimized for a traditional PC, and it’s not free for the full version. As an owner of many Android phones I can see how the many OS updates have proved to make the platform much better with more efficiency and less bugs, especially on the Lollipop release of Android.
With 53.3% (Fig. 1.) of the phone OS market share there are a few things that Android got right. The integration of Google Calendar is easy, useful, and free. Conversely, on a Windows phone, the integration of Microsoft Outlook is awkward, overly optimized for a traditional PC, and it’s not free for the full version. As an owner of many Android phones I can see how the many OS updates have proved to make the platform much better with more efficiency and less bugs, especially on the Lollipop release of Android.

 Windows 10 also introduces a function that allows you to utilize multiple desktops not just screen extensions, and this is a lot like Mission Control from Apple OS X. This will be a big benefit for business users, creative users, students, and people who do a lot of multitasking. The hot key shortcut to open a virtual desktop is: Windows key + Ctrl +D. Windows 10 also adds something new for gamers and graphics focused users, direct X12, which is a Microsoft proprietary graphics card decoder that communicates with and optimizes the many different graphics chips on thousands of computer models. It is the industry standard and that is why it’s used on the hugely popular X-Box. Windows 7 and 8.1 will not get access to direct X12 so graphics will be better on Windows 10. A creative person could even game in one desktop while they work in another assuming they have the RAM and CPU power needed for those specific applications – this is pretty cool. Another interesting visual add is the Windows Snap feature which allows you to split your screen into two, three or four separate areas and the hotkey shortcuts for this are:
Windows 10 also introduces a function that allows you to utilize multiple desktops not just screen extensions, and this is a lot like Mission Control from Apple OS X. This will be a big benefit for business users, creative users, students, and people who do a lot of multitasking. The hot key shortcut to open a virtual desktop is: Windows key + Ctrl +D. Windows 10 also adds something new for gamers and graphics focused users, direct X12, which is a Microsoft proprietary graphics card decoder that communicates with and optimizes the many different graphics chips on thousands of computer models. It is the industry standard and that is why it’s used on the hugely popular X-Box. Windows 7 and 8.1 will not get access to direct X12 so graphics will be better on Windows 10. A creative person could even game in one desktop while they work in another assuming they have the RAM and CPU power needed for those specific applications – this is pretty cool. Another interesting visual add is the Windows Snap feature which allows you to split your screen into two, three or four separate areas and the hotkey shortcuts for this are: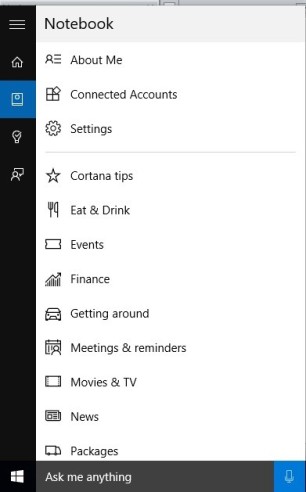 After upgrading to Window’s 10, we weren’t sure if we would use Cortana, but the more we use it the more we like it. In playing around with Cortana, you can provide feedback with screenshots that go right back to the teams at Microsoft. To prepare for the 10 release Microsoft was using an estimated five million external testers known as “insiders” to get this type of bug feedback. This impressive number is a considerable increase from prior releases. Cortana is easy to locate in the bottom left of the screen next to the start menu. We find that if the user types a question in the search bar it will add tips and give you interesting facts each and every day, if you let it. Cortana starts out giving you information on the weather, finance, and sports but you can customize this under notebook settings (Fig. 3). Cortana is very intuitive and can track things for you. If you’re receiving a package, it will tell you the progress or details of that package. Say you’re picking someone up at the airport, Cortana will tell you if the flight is on time.
After upgrading to Window’s 10, we weren’t sure if we would use Cortana, but the more we use it the more we like it. In playing around with Cortana, you can provide feedback with screenshots that go right back to the teams at Microsoft. To prepare for the 10 release Microsoft was using an estimated five million external testers known as “insiders” to get this type of bug feedback. This impressive number is a considerable increase from prior releases. Cortana is easy to locate in the bottom left of the screen next to the start menu. We find that if the user types a question in the search bar it will add tips and give you interesting facts each and every day, if you let it. Cortana starts out giving you information on the weather, finance, and sports but you can customize this under notebook settings (Fig. 3). Cortana is very intuitive and can track things for you. If you’re receiving a package, it will tell you the progress or details of that package. Say you’re picking someone up at the airport, Cortana will tell you if the flight is on time.


 This entrepreneurial effort is only likely to gain momentum and it shows that Chamberlin’s creativity is beyond music. In terms of the Smashing Pumpkins it shows that Billy Corgan is likely to tap Chamberlin’s business sense to help remake and remarket the Smashing Pumpkins since the band has been mostly a revolving door over the last 6 years. It will be much harder for Corgan to lose Chamberlin this time around as he has the ability to cross market the band’s shows via his company, even if it’s still in development mode. Corgan and Chamberlin truly could be at the beginning of a new music business nirvana but let’s hope egos and miscommunication do not get in the way of a reunion that has a history and talent that is worth much more than a small summer tour.
This entrepreneurial effort is only likely to gain momentum and it shows that Chamberlin’s creativity is beyond music. In terms of the Smashing Pumpkins it shows that Billy Corgan is likely to tap Chamberlin’s business sense to help remake and remarket the Smashing Pumpkins since the band has been mostly a revolving door over the last 6 years. It will be much harder for Corgan to lose Chamberlin this time around as he has the ability to cross market the band’s shows via his company, even if it’s still in development mode. Corgan and Chamberlin truly could be at the beginning of a new music business nirvana but let’s hope egos and miscommunication do not get in the way of a reunion that has a history and talent that is worth much more than a small summer tour.
 1) We knew there would come another well-positioned company who makes a pair of smart glasses like Google Glass and that it will derive more competition and innovation. Microsoft raised their hand right away with their HoloLens glasses which are hologram based, slightly “gamified”, and seemingly better than Google Glass largely because they tied it in with known Windows functionality (broader offerings). See a video of this cool new technology here:
1) We knew there would come another well-positioned company who makes a pair of smart glasses like Google Glass and that it will derive more competition and innovation. Microsoft raised their hand right away with their HoloLens glasses which are hologram based, slightly “gamified”, and seemingly better than Google Glass largely because they tied it in with known Windows functionality (broader offerings). See a video of this cool new technology here: There is no doubt that mobile will continue to grow and will be used on smaller devices like watches, ear buds, pacemakers, and contact lenses. Web design has shifted so fast to mobile that sometimes good web design and user experience is forgotten about for non-mobile users or business users who on average spend much more time on those same sites than mobile users. Thus a better balance of the two design types is needed, and an app is a separate project all together yet still needed. I also think Microsoft will take more mobile market share away from Android and Apple since they have learned a lot from their Windows 8 release and are quickly working to release Windows 10 as a better touch based mobility optimized O.S. that many are excited to try.
There is no doubt that mobile will continue to grow and will be used on smaller devices like watches, ear buds, pacemakers, and contact lenses. Web design has shifted so fast to mobile that sometimes good web design and user experience is forgotten about for non-mobile users or business users who on average spend much more time on those same sites than mobile users. Thus a better balance of the two design types is needed, and an app is a separate project all together yet still needed. I also think Microsoft will take more mobile market share away from Android and Apple since they have learned a lot from their Windows 8 release and are quickly working to release Windows 10 as a better touch based mobility optimized O.S. that many are excited to try.
 1) Stakeholder Management: Attain clear support from the executive stakeholders from the beginning of the project and schedule regular check-in meetings with them ahead of time as they tend to be very busy and are often pulled in many directions. Set the tone that their participation is needed and that they will need to approve change requests which is not uncommon. You should also use clever people skills and empathetic listening skills as you interview the many high-level stakeholders in the early part of the project so as to diffuse conflict and get consensus on disagreements about scope, business goals, order, and to find out who will be the thorn in your back as the sooner you know that the better. Also, accept that stakeholders will be different and they may not even directly work for your company which is ok as those ones tend to offer specialized expertise and are often very creative.
1) Stakeholder Management: Attain clear support from the executive stakeholders from the beginning of the project and schedule regular check-in meetings with them ahead of time as they tend to be very busy and are often pulled in many directions. Set the tone that their participation is needed and that they will need to approve change requests which is not uncommon. You should also use clever people skills and empathetic listening skills as you interview the many high-level stakeholders in the early part of the project so as to diffuse conflict and get consensus on disagreements about scope, business goals, order, and to find out who will be the thorn in your back as the sooner you know that the better. Also, accept that stakeholders will be different and they may not even directly work for your company which is ok as those ones tend to offer specialized expertise and are often very creative. 3) Quality Management: Having worked on many complex projects in highly regulated industries over the last 5 years I have noticed a shift towards agile methodologies vs. waterfall. From my perspective this is really about quality and timely flexibility. Aligning the project tasks in small pieces allows you to test the results independently and faster, and if the results are bad that’s a good thing because it’s just one piece of the project and you can learn from it – getting an early warning. Yet to get better quality out of an error you need to have documented what went into the error from beginning to end and you need intelligent consensus. On SDLC projects there will be many small errors which then raise questions about other systems and how they relate to the business rules. Yet with good process flows, screen shots, and JAD sessions with key people, you can ensure that these errors are nothing more than normal bumps in the road. Every project has its bumps but the real test is having above average quality on budget and on time at the projects end thus creating a reusable plan others can learn and be inspired from.
3) Quality Management: Having worked on many complex projects in highly regulated industries over the last 5 years I have noticed a shift towards agile methodologies vs. waterfall. From my perspective this is really about quality and timely flexibility. Aligning the project tasks in small pieces allows you to test the results independently and faster, and if the results are bad that’s a good thing because it’s just one piece of the project and you can learn from it – getting an early warning. Yet to get better quality out of an error you need to have documented what went into the error from beginning to end and you need intelligent consensus. On SDLC projects there will be many small errors which then raise questions about other systems and how they relate to the business rules. Yet with good process flows, screen shots, and JAD sessions with key people, you can ensure that these errors are nothing more than normal bumps in the road. Every project has its bumps but the real test is having above average quality on budget and on time at the projects end thus creating a reusable plan others can learn and be inspired from. 4) Risk Management: In this new era where almost everything is in the cloud and hackers are targeting large and mid-sized companies to steal and sell their data, every risk analysis document/plan should take into consideration data security, customer privacy, access controls from the project team, and there should be an independent audit plan – often out of scope of the project and done by a different group for checks and balances. No project has no data so data is always a part of a project, sometimes more and sometimes less. Question number one is who should have access to the data and at what point? In today’s environment you should embrace a need to know policy and you should document that to reduce risks. You should also imagine a worst case scenario and be prepared for it and run this by the executive project sponsors, and/or risk officer if your company has one.
4) Risk Management: In this new era where almost everything is in the cloud and hackers are targeting large and mid-sized companies to steal and sell their data, every risk analysis document/plan should take into consideration data security, customer privacy, access controls from the project team, and there should be an independent audit plan – often out of scope of the project and done by a different group for checks and balances. No project has no data so data is always a part of a project, sometimes more and sometimes less. Question number one is who should have access to the data and at what point? In today’s environment you should embrace a need to know policy and you should document that to reduce risks. You should also imagine a worst case scenario and be prepared for it and run this by the executive project sponsors, and/or risk officer if your company has one.


 The general consensus is that a HVAC contractor for Target, Fazio Mechanical Services, who had access to Target’s networks got their own networks hacked via an e-mail phishing attack, normally an elementary attack method; yet that attack installed malware that then got onto Target’s network and installed more malware that copied personal data from Target’s payment processing terminals when it was in the “working memory area” or “cache” of the software/system – that is before it gets encrypted to be sent to the bank to be authorized. This is part of the reason why it was not detected so fast and yes these hackers were smart.
The general consensus is that a HVAC contractor for Target, Fazio Mechanical Services, who had access to Target’s networks got their own networks hacked via an e-mail phishing attack, normally an elementary attack method; yet that attack installed malware that then got onto Target’s network and installed more malware that copied personal data from Target’s payment processing terminals when it was in the “working memory area” or “cache” of the software/system – that is before it gets encrypted to be sent to the bank to be authorized. This is part of the reason why it was not detected so fast and yes these hackers were smart.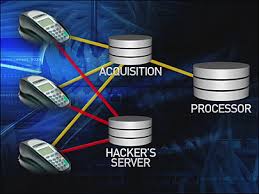 Yet Target did not take this alert seriously but why? Fear of change, ego, poor leadership, and too much bureaucracy got in the way of the costly software’s effectiveness. At the time of the breach FireEye was a new software tool for Target’s technology group and what I know about new technology is that people delay embracing and learning new systems of out of fear that those systems will be buggy or not as good as the old ones. I understand this very well having worked part time in the P.C. dept. at Best Buy for more than 3.7 years representing Intel and related software makers Microsoft, Symantec, Trend Micro, and Adobe. When Windows 8 came out all kinds of people were doubting it not because it was bad but because it was more work to get to know, and if they saw something really different about it, they were inclined to think it was a bug when in fact it was a useful design feature they didn’t yet understand. The same bias can be applied to Apple computers. People falsely think that they are immune from viruses because Apple designs them that way. What a joke. Apple computers are only as secure as their understanding of the latest virus. Yes it is true the Apple operating system is not targeted as much for viruses but it is also not used as much and it is hardly used by large companies and governments.
Yet Target did not take this alert seriously but why? Fear of change, ego, poor leadership, and too much bureaucracy got in the way of the costly software’s effectiveness. At the time of the breach FireEye was a new software tool for Target’s technology group and what I know about new technology is that people delay embracing and learning new systems of out of fear that those systems will be buggy or not as good as the old ones. I understand this very well having worked part time in the P.C. dept. at Best Buy for more than 3.7 years representing Intel and related software makers Microsoft, Symantec, Trend Micro, and Adobe. When Windows 8 came out all kinds of people were doubting it not because it was bad but because it was more work to get to know, and if they saw something really different about it, they were inclined to think it was a bug when in fact it was a useful design feature they didn’t yet understand. The same bias can be applied to Apple computers. People falsely think that they are immune from viruses because Apple designs them that way. What a joke. Apple computers are only as secure as their understanding of the latest virus. Yes it is true the Apple operating system is not targeted as much for viruses but it is also not used as much and it is hardly used by large companies and governments.

 Although Prince is no lawyer, he has hired some great ones over the years, L. Londell Mcmillan – the famous entertainment lawyer and owner of the Source R&B Magazine, and Clive Davis – the Harvard Law educated record mogul, chart-topping producer, and long time record company CEO at Sony, Arista, and J records. Prince’s legal and business maneuvers have helped him win a legal case against his estranged half-sister, got him out of an unfavorable contract with Warner Bros in 1996 to redefine his brand under a new name thus renewing interest in his art, allowed him an open record deal at Arista Records in 1999, and in 2004 his business team came up with the idea to sell his album with each concert ticket sold for his large worldwide Musicology arena tour thus bringing his album sales numbers to the top of the Sound Scan charts in an unprecedented move. Yet Prince like the King / Elvis has lost a few battles, mostly due to his poor management style and huge ego. In one case a European court ordered him to pay $2.95 million dollars to a European concert promoted he stiffed — for good or bad reasons – Prince is indeed battle-tested. Yet presently he has renegotiated a new contract with Warner Bros to re-master and remarket Purple Rain and many of his best albums of years ago and for the most part, he gets the rights to the masters which is unheard of for most artists. Purple Rain helped broaden free speech in music for today, brought about “explicit lyrics” stickers, and encouraged multiculturalism in a band that has mass appeal.
Although Prince is no lawyer, he has hired some great ones over the years, L. Londell Mcmillan – the famous entertainment lawyer and owner of the Source R&B Magazine, and Clive Davis – the Harvard Law educated record mogul, chart-topping producer, and long time record company CEO at Sony, Arista, and J records. Prince’s legal and business maneuvers have helped him win a legal case against his estranged half-sister, got him out of an unfavorable contract with Warner Bros in 1996 to redefine his brand under a new name thus renewing interest in his art, allowed him an open record deal at Arista Records in 1999, and in 2004 his business team came up with the idea to sell his album with each concert ticket sold for his large worldwide Musicology arena tour thus bringing his album sales numbers to the top of the Sound Scan charts in an unprecedented move. Yet Prince like the King / Elvis has lost a few battles, mostly due to his poor management style and huge ego. In one case a European court ordered him to pay $2.95 million dollars to a European concert promoted he stiffed — for good or bad reasons – Prince is indeed battle-tested. Yet presently he has renegotiated a new contract with Warner Bros to re-master and remarket Purple Rain and many of his best albums of years ago and for the most part, he gets the rights to the masters which is unheard of for most artists. Purple Rain helped broaden free speech in music for today, brought about “explicit lyrics” stickers, and encouraged multiculturalism in a band that has mass appeal.