The 11th edition of the DBIR (Data Breach Investigation Report) was released this month. It analyzed more than 53,000 cybersecurity incidents and over 2,200 data breaches across the globe. Here is a summary of its key findings:
 Ransomware continues to be a top cybersecurity threat, according to the report. Ransomware is found in almost 39 % of malware attacks – double the amount in last year’s analysis. “Ransomware remains a significant threat for companies of all sizes,” says Bryan Sartin, executive director security professional services, Verizon. “It is now the most prevalent form of malware, and its use has increased significantly over recent years.” This comes as no surprise to many city and state officials that have battled with ransomware takeovers recently. Systems in the city of Atlanta were offline for several days last month following a ransomware attack. Government offices and municipal systems have also been targeted in Baltimore, North Carolina, San Francisco, and others yet to come forward – the government does not like to admit their errors.
Ransomware continues to be a top cybersecurity threat, according to the report. Ransomware is found in almost 39 % of malware attacks – double the amount in last year’s analysis. “Ransomware remains a significant threat for companies of all sizes,” says Bryan Sartin, executive director security professional services, Verizon. “It is now the most prevalent form of malware, and its use has increased significantly over recent years.” This comes as no surprise to many city and state officials that have battled with ransomware takeovers recently. Systems in the city of Atlanta were offline for several days last month following a ransomware attack. Government offices and municipal systems have also been targeted in Baltimore, North Carolina, San Francisco, and others yet to come forward – the government does not like to admit their errors.
The report also shows that attacks on public sector organizations continue to focus on espionage. 43 % of public sector attacks were motivated by espionage. Of those attacks, 61 % were carried out by state-affiliated actors. Privilege misuse and error by insiders account for a third of breaches. Small businesses represent 58 percent of data breach victims. Over 50% of the attacks on public sector organizations were accomplished using backdoors in software, which arguably makes the case for why putting backdoors in software is a bad idea even if a government plans to use it for its own purposes – the government is far behind the private sector in incubating innovation here. Using phishing techniques to get data from individuals remains the most popular method as individuals continue to be the weakest link when it comes to security.
Fig 1. Data Breach Causes, Verzion 2018
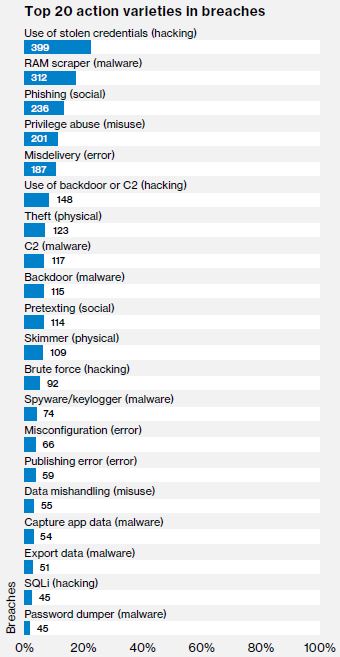 Using stolen credentials topped the list of causes for data breaches (See Fig 1. for the other top causes). A common saying is “it’s easier to ask the employee for their password than try to guess it”, so social engineering continues to be a very useful tactic for hackers. For most employees, the only security protection system is their password. If a cyber-criminal obtains it, they can easily bypass most of the company’s security controls.
Using stolen credentials topped the list of causes for data breaches (See Fig 1. for the other top causes). A common saying is “it’s easier to ask the employee for their password than try to guess it”, so social engineering continues to be a very useful tactic for hackers. For most employees, the only security protection system is their password. If a cyber-criminal obtains it, they can easily bypass most of the company’s security controls.
Attribution is probably one of the most difficult tasks in cyber-crime which already has more challenges than most people realize, with misdirection and lack of digital footprints to help lead to the cyber-criminal. This is likely due to several virtual machines and botnets used to facilitate the attack across several nations – all of which are likely unfriendly to the United States. Specifically, 73% of cyber-attacks were caused by outsiders. Organized crime rings are very likely using hackers as a service because 50% of cyber-attacks were attributed to organized crime. 12% was attributed to nation-states – APT (advanced persistent threats) who have unlimited funds.
Specific to Healthcare: The healthcare industry is rife with error and misuse. In fact, it is the only industry that has more internal actors behind breaches than external. In addition to these problem areas, ransomware is endemic in the industry—it accounts for 85 % of all malware in healthcare.
In total, there were 750 incidents and 536 with confirmed data disclosed. The top three patterns include: miscellaneous errors, crimeware, privilege misuse – 63 % of all incidents within healthcare. Breach threat actors breakdown: 56 % internal, 43 % external, 4 % partner, 2 % multiple parties. Breach actor motives are: 75 % financial, 13 % fun, 5 % convenience, Data compromised: 79 % medical, 37 % personal, 4 % payment.
The full report is available here.
Abstract Forward Consulting can help you review the issues in this report to build stronger security and process controls. Contact us here to learn more.
Jeremy Swenson, MBA, MSST

